Summary
- Australians lost over AU$634 million to scams in 2019, according to the Australian Competition and Consumer Commission's (ACCC) Targeting Scams 2019 report.
- In the wake of cybercrime, phishing and spear-phishing are the most common threats.
- Stolen data from businesses and government portals are auctioned on the Dark Web.
- According to the US Privacy Affairs Dark Web Price Index, the average cost of a hacked Facebook is US$55.
- Cybercriminals are looking for vulnerabilities and weaknesses in systems and networks; adequate cybersecurity measures are a must.
Cybercrime is one of the most prevalent risks and threats facing Australia security mechanism. The incidence, magnitude, and complexity of cyber activities against Australia's national and economic interest are increasing. In the wave of cybercrime, phishing and spear-phishing are the most common threat individuals, government agencies and companies are facing.
Stealing personal information or user credentials and gaining access to the networks or distributing malicious content are some standard methods cybercriminals are using. Stolen data from businesses and government portals are auctioned on the Dark Web.
The lucrative underground marketplace offers cybercrime-as-a-service (CaaS) or access to high-end hacking tools readily on the dark web. These systems were only available to national states before. These marketplaces also offer valuable cybercrime enablers. Personal information and other sensitive data like compromised user credentials are available in the dark web marketplace.
GOOD READ: Cyber Espionage Campaign: Strings that tie China, Australia and the US
Cybercriminals Follow the Money
The ACSC Annual Cyber Threat Report (July 2019 to June 2020) states that according to the Australian Competition and Consumer Commission's (ACCC) Targeting Scams 2019 report, Australians lost over AU$634 mn to scams in 2019.
The ACSC report mentions that cybercriminals follow the money. Australia's relative wealth and increasing delivery of services through online channels are attractive and profitable for the cybercriminals. Transnational cybercriminals and their affiliates are particularly of concern, as they develop, share, sell and use sophisticated tools and techniques to commit the cybercrimes.
The actual cost of cybercrime to the Australian economy is challenging to quantify. The industry estimates have previously placed annual cybersecurity incidents at AU$29 bn.
According to the US Privacy Affairs Dark Web Price Index, the average cost of a stolen Facebook account is US$55. Stolen online banking logins (minimum US$2000 on an account) cost US$65, and PayPal transfers from the stolen account for more than US$3000 cost as low as US$155.94.
Why is this data necessary? Because a lot of individuals and businesses are facing cyberattacks and the information is being sold on Dark Web marketplace.
RELATED READ: Cybersecurity and the Requirement of a Resilient Environment in Australia
Cyberattack on Service NSW
Around 186K Australians’ personal details have been accessed by hackers in a cyberattack on Service NSW. Hackers targeted the email accounts of 47 staff members and gained illegal access to around 3.8 mn documents in the month of May.
The review conducted after the cyberattack found 500K documents which referenced the personal information of 186K customers.
Service NSW is the New South Wales Government executive agency where we can get a permit, register a birth, pay fines, apply for a licence, etc.
Not just the companies, but Australia's top-ranked educational institutes also faced cybercrimes hackers breached their cyber defenses. The criminals stole sensitive data of students, including their bank account numbers and passport details.
GOOD READ: Cybersecurity and the Requirement of a Resilient Environment in Australia
Regis Healthcare: Business Continuity Plan Helped Sail Through Cyberattack
In the month of August, Regis Healthcare Limited (ASX:REG) was targeted in a cyberattack by an overseas third party. The company implemented its back-up and business continuity system; hence the attack did not affect the delivery of resident care or services.
The incident was immediately reported to the Australian Cyber Security Centre, the Office of the Australian Information Commissioner, and other regulatory bodies.
But the attackers copied some data from the company's IT system and released some personal data in the public domain. Regis Healthcare had contacted the other parties whose personal data was publicly released.
RELATED READ: Knock Knock! Cybercriminal at Your Doorstep
REvil ransomware attack
Melbourne-based contract formulation and packing company Chem Pack recently faced a REvil ransomware attack, and its data was being allegedly sold on the dark web.
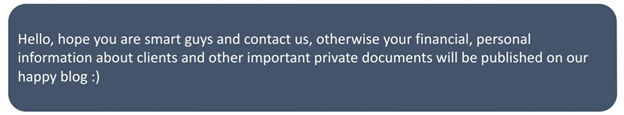
According to the cybersecurity firm Secureworks, REvil (also known as Sodinokibi ransomware) was first identified last year on the dark web. The ransomware is used by the financially motivated GOLD SOUTHFIELD threat group. The first information of REvil came into light when it exploited vulnerabilities in Oracle WebLogic.
Story of Lion Australia: Systematic Cyber Attack
In June, Lion Australia, a beverage and food company which operates in Australia and New Zealand and a subsidiary of Japanese beverage giant Kirin, faced a systematic cyber attack. The ransomware attack caused a partial IT outage. Notably, Lion continued to make progress in restoring the key systems despite the cyber attack.
The company said that the hospitality industry had been trying to get back on its feet after the COVID-19 disruption. The series of ransomware attacks are turning out to be challenging for Lion and its industry partners. The company said that they did not have any evidence of the data being removed. But the data from the system could be stolen and may be disclosed in the future.
Bottom line:
The cyberattacks have subsequently increased in the last few months, and cybercriminals are looking for vulnerabilities and weaknesses in systems and networks. It is important to apply adequate cybersecurity measures as individuals, business owners and government agencies.



